Layer One: In-Transit Cargo Access
The most visible layer is the door — swing doors on dry van and refrigerated trailers, roll-up doors on last-mile and distribution units. Most fleets have something here. The question is whether what they have actually holds up to a determined attack.
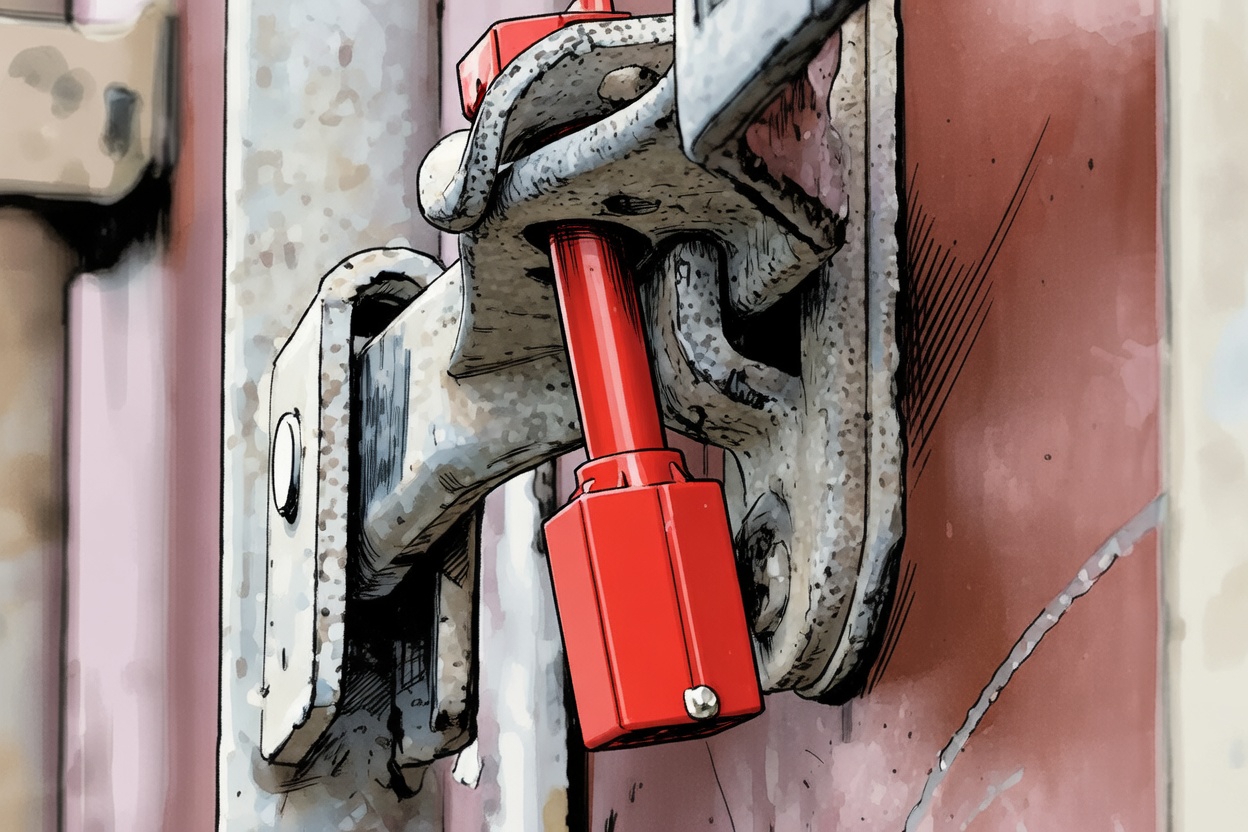
A padlock on a swing door is a starting point, not a security program. Without a hasp that covers the padlock body, the padlock shackle is accessible for a sawing or cutting attack. Without a hasp that is itself bolted with hardened fasteners and shields both the active and passive doors, prying a door apart is achievable in under a minute. The right answer for a swing door is the combination: a padlock with a boron steel shackle and a tamper-resistant cylinder, mounted through a heavy-gauge hasp that blocks direct access to the padlock itself. These products exist to work together. Buying them separately and hoping for the best is not the same as deploying a layered system.
For roll-up doors, the single most effective change a fleet can make is moving to a slam-lock mechanism. A slam-lock engages automatically when the door closes. There is no step for the driver to miss, no padlock to forget, no window of vulnerability at every stop. The door closes. It locks. Every time. Fleets that have made this change universally report that driver compliance is no longer a variable in their security equation, because compliance is no longer required.
The third element of the in-transit layer is often overlooked entirely: seal integrity. For carriers subject to shipper seal requirements — food, pharmaceutical, high-value retail — a tampered or broken seal triggers a load refusal, regardless of whether the cargo is intact. Protecting the seal from tampering is not a separate program from physical security. It is part of the same layered approach. A seal guard that mounts to the door hardware and shields the seal from tampering, paired with ISO 17712 H certified seals, closes a gap that locks alone cannot address.
Why TAPA TSR and C-TPAT emphasize the physical layer
Both TAPA's Trucking Security Requirements and C-TPAT's Minimum Security Criteria call for documented, consistent physical security controls on cargo-carrying vehicles. Auditors are not looking for the most expensive lock — they are looking for a systematic approach. Can the carrier demonstrate that every vehicle in scope has defined physical security coverage? Can they show that key control is managed, hardware is standardized, and that the program can be replicated at a new terminal? That kind of documentation requires a program, not a parts list.
Layer Two: Dropped and Unattended Trailer Security
Industry data consistently shows that a large share of trailer theft happens when equipment is stationary, whether at a yard, distribution center, rest stop, or along a route. A dropped trailer without physical protection can be removed quickly by anyone with access to a tractor.
For dropped and unattended trailers, fleets typically begin by securing against unauthorized movement. A king pin lock prevents a tractor from coupling to the trailer, while a landing gear lock prevents the trailer from being raised for hookup. Either control creates an immediate physical barrier that forces time, effort, and added visibility into any theft attempt.
Some operations add a glad hand lock as another layer, securing the air brake connection so brake pressure cannot be established and the trailer cannot be released in the normal way.
The right combination depends on how the equipment is used, where it is left unattended, and the level of exposure involved. Even one properly applied lock changes the equation. Layering controls where risk justifies it makes a trailer far less attractive to anyone looking for quick access and an easy departure.
Opportunistic thieves will move on. Organized operations need time and tools. Remove both.
Layer Three: Tractor Immobilization
Tractor theft is a separate threat from cargo theft, but the two are often connected: a stolen tractor becomes the vehicle used to move a stolen trailer. Fleet security programs that address cargo access and yard security but ignore tractor immobilization are leaving the third leg of the triangle unprotected.
The most effective tractor immobilization tool is an air cuff lock that covers the dash-mounted air valve levers — the controls that release the parking brakes and allow the vehicle to move. With the air cuff in place, no one can release the brakes without the corresponding key. The truck cannot be moved. There is no bypass, no workaround available with standard tools, and no modification required to the vehicle. The device is portable, moves with the driver, and is keyed to the fleet's existing key control system.
For overnight parking, rest stops, and any situation where a driver is away from the cab for an extended period, this is the most direct available control against tractor theft and unauthorized movement.
The Standardization Imperative
Layering physical controls across three operational contexts is the right framework. But the framework only works if it is applied consistently. One terminal with a rigorous physical security program and another with hardware store padlocks is still a vulnerable fleet. Cargo theft operations are sophisticated enough to identify the weak point in a distribution network and target it specifically.
Standardization across a fleet requires two things: a defined hardware specification for each layer, and a key control program that manages who has access to what. A master key system allows fleet management to hold a single key that operates all locks across all terminals, while individual drivers carry keys that work only on their assigned assets. When a driver leaves, their key access ends. No key can be commercially duplicated — the key system is restricted, and the only source for new keys or rekeying is the security hardware supplier.
This level of control is not a luxury for large enterprise fleets. It is the baseline expectation for any carrier that wants to make a credible claim to shippers, insurers, and auditors that their physical security program is managed, documented, and consistent.
A note on the relationship between physical and technological controls
GPS tracking, load monitoring sensors, and camera systems are valuable components of a fleet security program. They create visibility and generate evidence. What they do not do is prevent access — a GPS tracker in a stolen load still means a stolen load. The strongest programs treat physical controls as the prevention layer and technology as the detection and recovery layer. Both matter. The mistake is investing heavily in detection while under-investing in prevention.
Where to Start
For most fleets, the path to a fully layered physical security program does not require replacing everything at once. It requires an honest assessment of where the gaps are:
- Are swing door trailers protected at the door and the padlock, or just the padlock?
- Do roll-up door trailers lock automatically, or does security depend on driver behavior at every stop?
- Are seals protected from tampering, and are those seals certified to the standard your shippers require?
- Are dropped trailers secured against hookup, against landing gear operation, and against brake release, or just one of the three?
- Is there a tractor immobilization control in place for overnight and rest stop parking?
- Is the key control program documented, restricted, and consistent across terminals?
The gaps in that assessment are the starting point. Physical security improvements are among the most immediate, most measurable, and most durable investments a fleet can make in its security program. The hardware does not require maintenance, does not go offline, and does not generate false alerts. It just works, every shift, every terminal, every trailer.
Talk to TSI About Your Fleet's Physical Security Program
Transport Security, Inc. has spent over 40 years helping enterprise fleets build physical security programs that hold up in the field. We offer no-cost fleet security consultations to help security directors assess their current coverage, identify gaps, and build a standardized hardware program that works for their operation.